Creating.
Communicating.
Connecting.
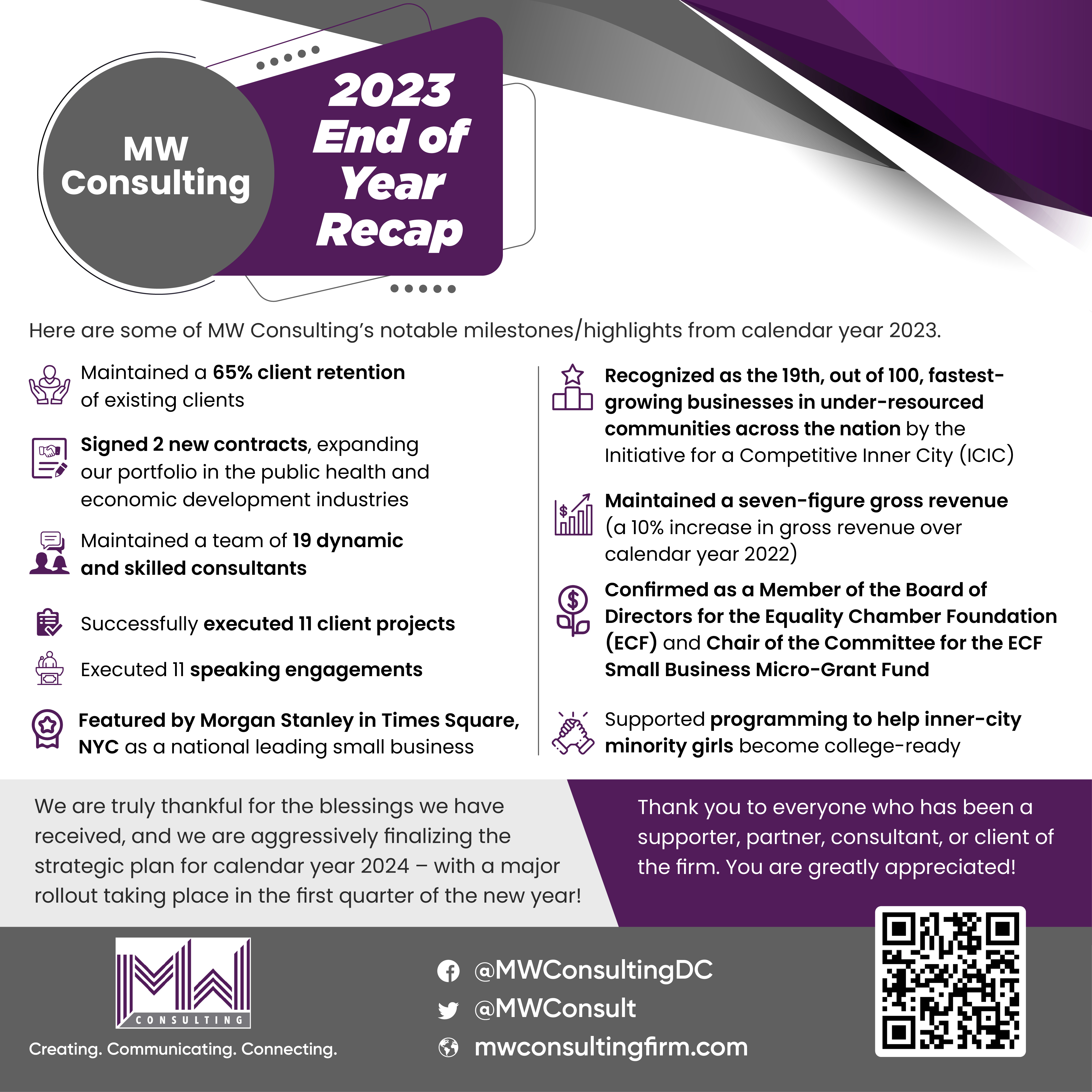
MW Consulting (MWC) empowers clients to create meaningful connections with stakeholders through compelling storytelling, dynamic visuals, and strategic engagement. Our team’s full-service approach delivers tailored communications solutions that strengthen both internal and external messaging, supported by practical technology tools to enhance outreach and efficiency.

We have supported 60+ clients, executing over 147 projects, across 12 industries, reaching 28 million individuals and 30+ stakeholder groups.

Areas of expertise
Our expert team crafts compelling stories, designs striking visuals, executes strategic plans, and delivers cutting-edge tech solutions to elevate communications.

Strategic Messaging and Storytelling
Crafting messages that resonate with diverse audiences.

Visuals
Creating stunning visuals that amplify your brand identity.

Public Relations
Boost your brand’s reputation and visibility with expert PR services.

Technology Solutions
Streamline operations and enhance efficiency with tailored IT solutions.

Certifications
Certified to work with Fortune 500 companies, national nonprofits, and federal & DC governments.
 Minority Business Enterprise (MBE) – National Minority Supplier Diversity Council | Certified Business Enterprised (CBE) – DC Department of Small and Local Business Development |
Lesbian, Gay, Bisexual and Transgender Business Enterprise (LGBTE) – National Gay & Lesbian Chamber of Commerce | Historically Underutilized Business Zone (HUBZone) – United States Business Administration |
 Small Local Business Enterprise (SLBE) – Metropolitan Washington Airports Authority (Airports Authority) |

Discover our unique edge
What our clients say about us
We work with those we wholeheartedly admire
Our team’s unique backgrounds and perspectives drive authentic, balanced, and innovative solutions that deeply connect with the communities we serve.